安恒月赛被暴打呜呜呜
呜呜呜,不仅做不成题还倒扣我分

emmm放错了

V神tql
这次边hvv边打CTF,效率有些低,没有akmisc后看其他项呜呜呜
MISC
签到
Description
异世相遇!尽享美味!安恒赛高!
去厕所喊出来语音识别就可以得到flag
flag
DASCTF{welcome_to_march_dasctf} 简单的png隐写
Analyze
开局一个压缩包,啥都没,fuzz得知是伪加密,解压后两张图,一个是我老婆(嗯

另一个是hint.png
010查看hint.png发现
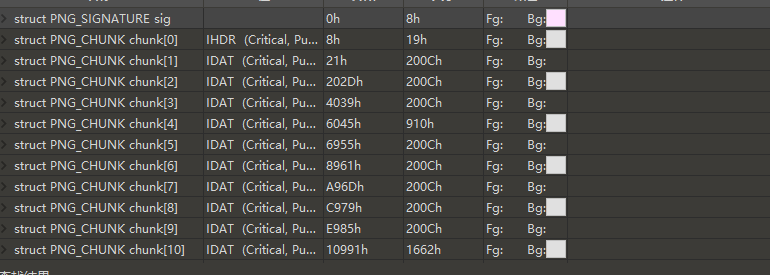
这数据块本来结束了,结果又开始满chunk,所以猜测其为两张图,给他加上头尾得到第二张图
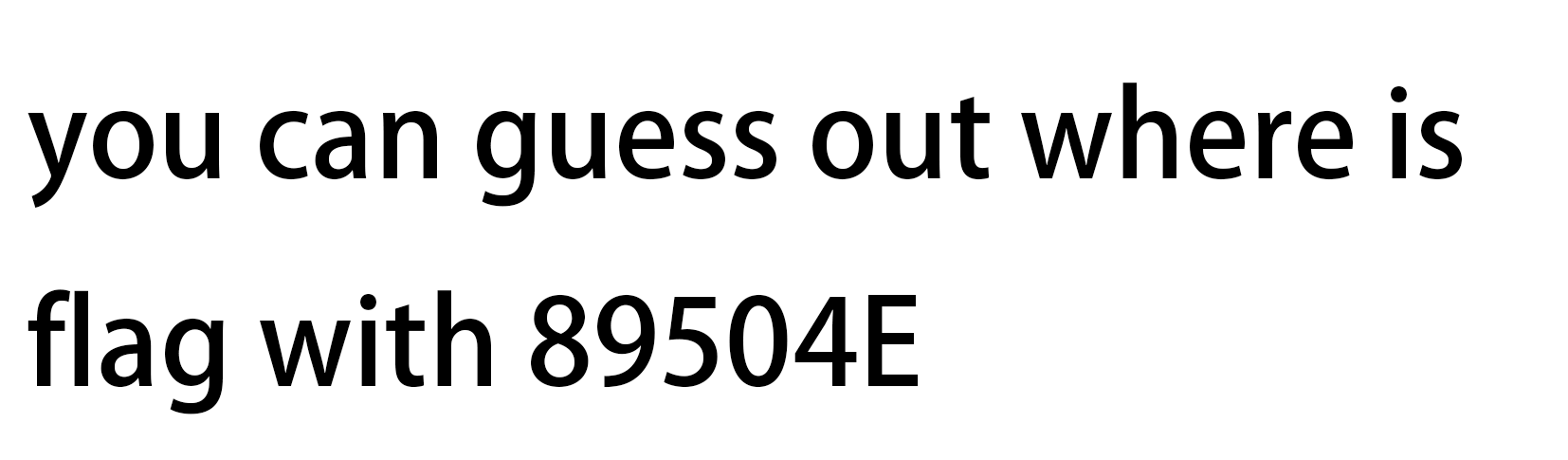
然后是谜语人时间guess out猜测得到outguess隐写,后面的89504E为密钥,得到MUY4QjA4MDg5MTgwNzg1RTAwMDM2NjZDNjE2NzJFNzQ3ODc0MDA0QkNCNDk0Q0FGMzZCMDMwMzQ0RDM1NDlCNjRDMzMzNTMzMzRCMTQ4MzVCNzQ4NEEzNTMzNDg0OTMyMzU0QjRFMzUzMTQ5MzFCNUFDRTVFMjAyMDA0NjhCMjIzRjI4MDAwMDAw然后cyberchef一把梭得到flag
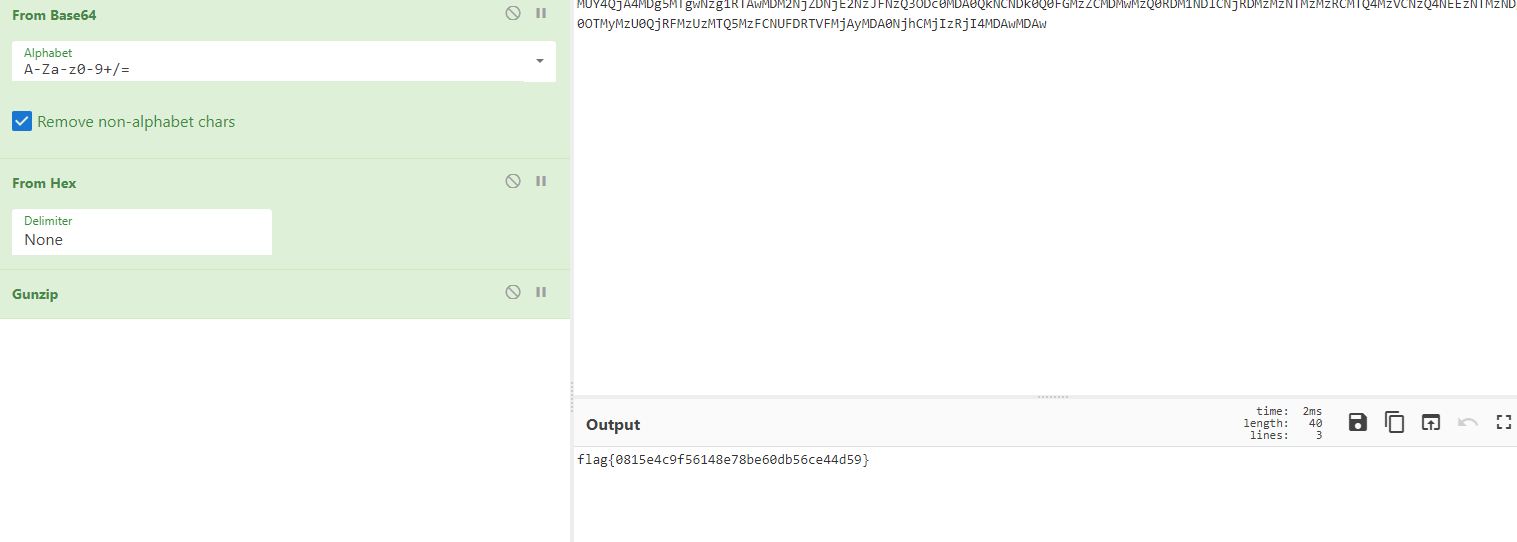
flag
flag{0815e4c9f56148e78be60db56ce44d59}雾都孤儿
Description
雾都孤儿
Analyze
孤儿题。。。脑洞多
首先解压得到一个docx和png
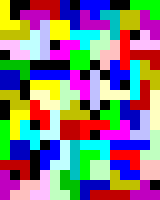
然后之前有见过这种图片,为一种npiet的图片编程语言,解出来喂Tetris,然后因为上一题的影响以及文档中只有一个图片,解压找到原图

outguess的密钥就为Tetris,得到一串编码
100000001001
11010101110
10000001101
100000001010
110101010
1101010110111
100000001000
110101010
0001
0100
11011
11010100110
110101000
11011
11010100110
11010101111
1100100
101101
101101
1001
101110
11010100110
100000001001
0100
101111
11010110
001
0101
11011
11010100110
11011
001
101111
0000
001
1010
11010100110
1000000111
1000000111
110101011000因为被信息论与编码折磨过一段时间,不难发现其可能是自制编码,稍微尝试了一下得知其为哈夫曼编码,唯一没有用上的就是文本了,所以我们将文本提出,再根据字频来进行哈夫曼编码。所以这里网上找了个哈夫曼脚本,之后一把梭即可得到flag。
Solve
#Huffman Encoding
#Tree-Node Type
import random
class Node:
def __init__(self,freq):
self.left = None
self.right = None
self.father = None
self.freq = freq
def isLeft(self):
return self.father.left == self
#create nodes创建叶子节点
def createNodes(freqs):
return [Node(freq) for freq in freqs]
#create Huffman-Tree创建Huffman树
def createHuffmanTree(nodes):
queue = nodes[:]
print(queue) #一个个node的地址
#每次对queue进行排序,
while len(queue) > 1:
queue.sort(key=lambda item:item.freq) #reverse = false
node_left = queue.pop(0)
node_right = queue.pop(0)
node_father = Node(node_left.freq + node_right.freq)
node_father.left = node_left
node_father.right = node_right
node_left.father = node_father
node_right.father = node_father
queue.append(node_father)
queue[0].father = None
return queue[0]
#Huffman编码
def huffmanEncoding(nodes,root):
codes = [''] * len(nodes)
for i in range(len(nodes)):
node_tmp = nodes[i]
while node_tmp != root:
if node_tmp.isLeft():
codes[i] = '0' + codes[i]
else:
codes[i] = '1' + codes[i]
node_tmp = node_tmp.father
return codes
def freq_count(strr):
chars = []
chars_fre = []
for i in range(len(strr)):
if strr[i] in chars:
pass
else:
chars.append(strr[i])
char_fre = (strr[i], strr.count(strr[i]))
# print(chars_fre)
chars_fre.append(char_fre)
return chars_fre
def encoder_huffman(strr,chars_fre,codes):
huffmans=''
for word in strr:
i = 0
#用于与code【i】还有item 的符号一一对应
for item in chars_fre:
if word == item[0]:
huffmans += codes[i]
i += 1
print(huffmans)
return huffmans
def decode_huffman(huffmans,codes,chars_fre):
original_code=''
while huffmans!='':
i=0
for item in codes:
if item in huffmans:
if huffmans.index(item) ==0:
original_code += chars_fre[i][0]
huffmans=huffmans[len(item):]
i+=1
return original_code
#chars = ['A','B','C','D','E','F','G','H','I','J','K','L','M','N']
#freqs = [10,4,2,5,3,4,2,6,4,4,3,7,9,6]
#元组的列表,item【1】就是后面2,2,3,4,等,生成器然后是作为列表保存,传入createnodes中
# ''''''chars_freqs = [('C', 2), ('G', 2), ('E', 3), ('K', 3), ('B', 4),
# ('F', 4), ('I', 4), ('J', 4), ('D', 5), ('H', 6),
# ('N', 6), ('L', 7), ('M', 9), ('A', 10)]
# ''''''
if __name__ =='__main__':
#sttttt =input('input your text')
#sttttt=input('input your text')
sttttt=""
sttttt = open('docx复制粘贴出来的文本','r').read()
# for i in range(100):
# sttttt += str(int(random.randint(27, 70)))
# sttttt += random.choice('abcdefghijklmnopqrstuvwxyz!@#$%^&*()')
# sttttt=random.sample(
# ['z', 'y', 'x', 'w', 'v', 'u', 't', 's', 'r', 'q', 'p', 'o', 'n', 'm', 'l', 'k', 'j', 'i', 'h', 'g', 'f', 'e',
# 'd', 'c', 'b', 'a'],20)
# print(sttttt)
# print('编译前输入的文本: '+sttttt)
#chars_freqs=freq_count(sttttt)
#c=input('input your word and freq, splitted with ,')
#splitt = c.split(',')
#print(splitt)
chars_freqs =[]
chars_freqs = freq_count(sttttt)
print('文本中字符的统计如下:\n'+str(chars_freqs))
# for i in range(0,len(sttttt),2):
# chars_freq= (sttttt[i], sttttt[i+1])
# if sttttt[i] in [item[0] for item in chars_freqs]:
# print('can not be a huffman code, there is some word repeating in this sentence, the huffman code will be without:',sttttt[i],sttttt[i+1])
# continue
# chars_freqs.append(chars_freq)
# print(chars_freqs)
nodes = createNodes([item[1] for item in chars_freqs])
#print([item[1] for item in chars_freqs])
root = createHuffmanTree(nodes)
codes = huffmanEncoding(nodes,root)
res = {}
for item in zip(chars_freqs,codes):
print ('Character:%s freq:%-2d encoding: %s' % (item[0][0],item[0][1],item[1]))
res.update({item[1]:item[0][0]})
# huffman_code=encoder_huffman(sttttt,chars_freqs,codes)
# print('转换之后的huffman编码 '+huffman_code)
# print('解码之后的原来的文本: '+decode_huffman(huffman_code,codes,chars_freqs))
print(res)
d2 = open('你outguess提取出来的编码','r').readlines()
re = ''
for i in d2:
re+=res[i[:-1]]
# re += res[i]
print(re)flag
DASCTF{This_Is_Hvffam_Dickens_secret_!!}小田的秘密
Analyze
开局一个流量包和一个zip,容易想到再流量包里找密码
流量包中有一个上传十分可疑,
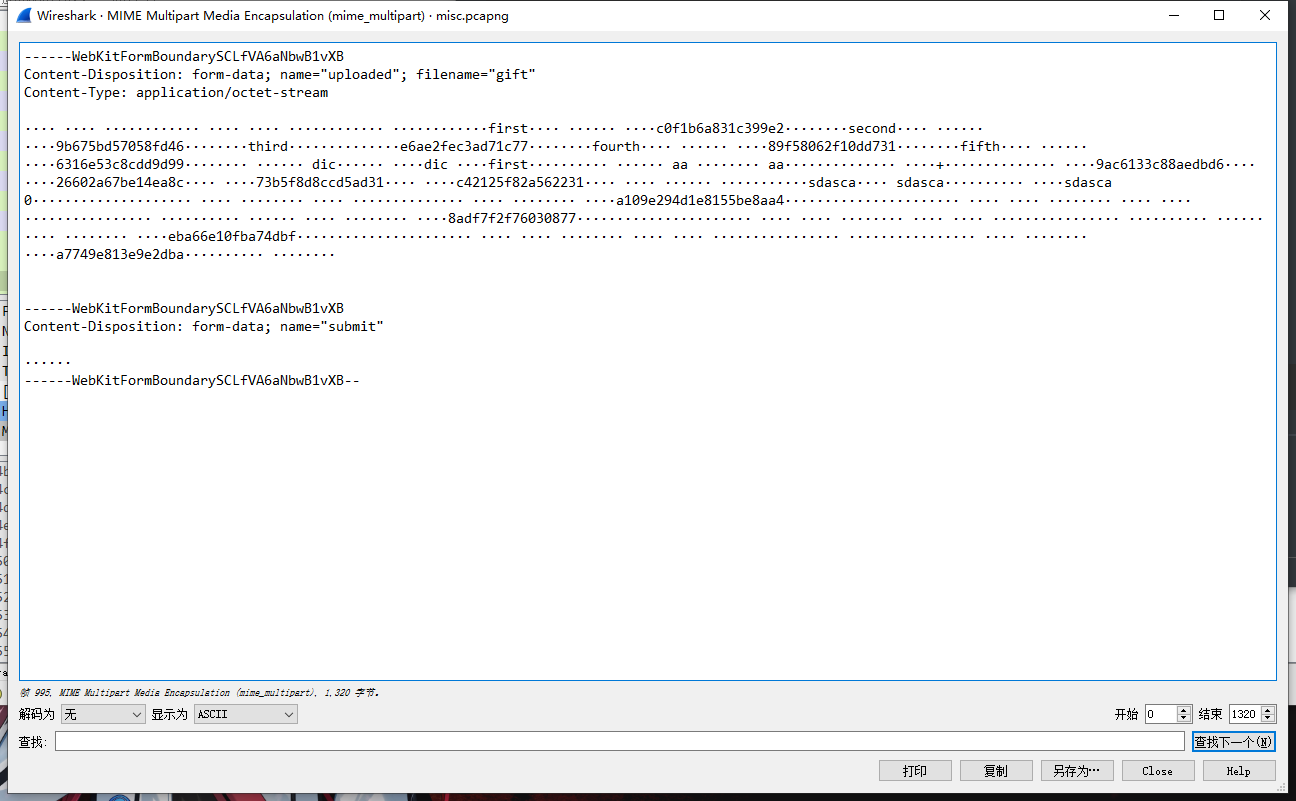
提起出来之后发现为
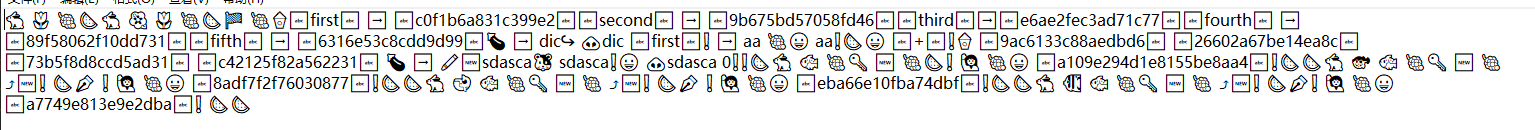
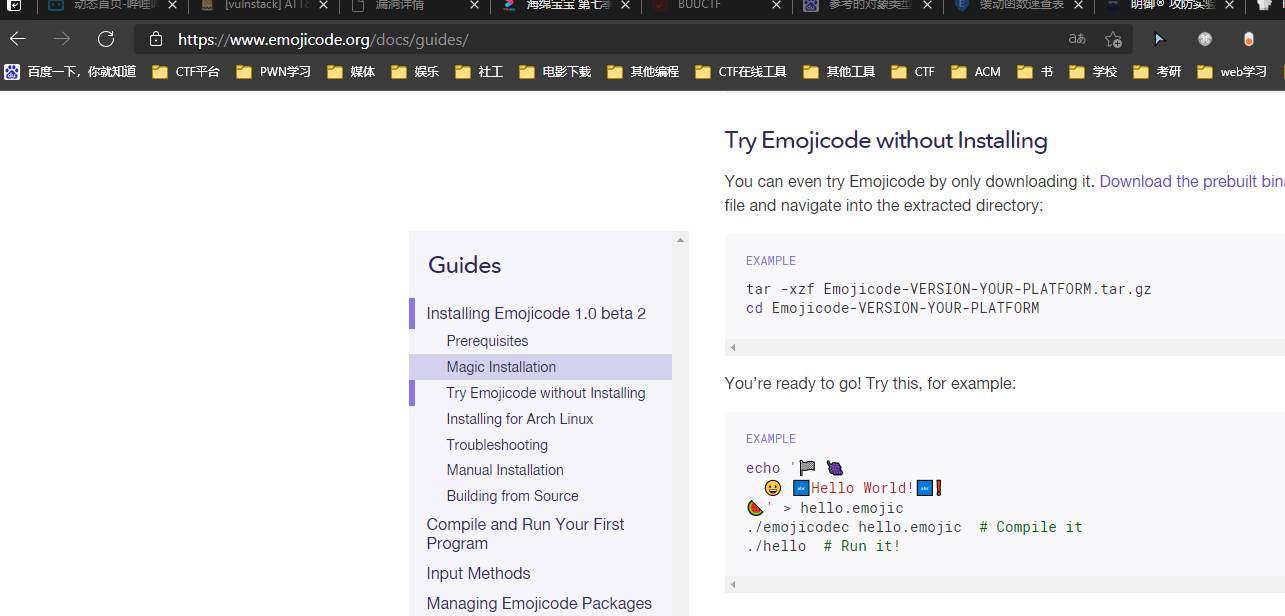
其为某种emoji有关的东西,上网fuzz一波找到其为一种编程语言emojicode
下载工具编译后得到解压密码c0f1b6a831c399e226602a67be14ea8c(PS:得多尝试几次,输出key不一定
解压后又是两个文件,64和flag.rar,64查询后得知是一种Commodore 64的语言,在线打一遍
得到NOT AN EGG解密得到flag
flag
6bffd0d9321df3c229cdff714bb5a0b0